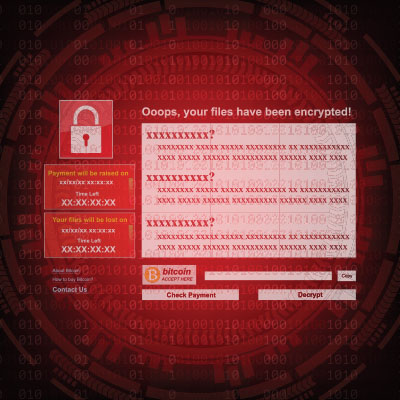
As business computing goes, ransomware poses the most significant threat. That’s why it’s imperative for organizations to proactively address this menace head-on. Today, we propose a comprehensive three-part strategy that can help your organization sidestep ransomware.
Ransomware is a real problem; I mean, a real problem. Not only does it create serious problems for any organization that is victimized by it, it is about to be a completely pervasive problem for everyone. It is extremely important for your organization to take the threat of ransomware seriously by implementing a strategy to keep it from being an issue. Today, we offer a three-pronged approach to doing just that.
It’s easy to think of email as something that just works. You open up Outlook or log into Gmail and your mail is there. Most people aren’t even aware of the vast, complex set of systems required for email to even work—and we don’t blame you. It’s extremely complicated. That being said, if nobody is actively managing your email, providing protection for the underlying technology, and making sure that it was and remains configured properly, it’s possible that your email could be working fine while opening you up for unseen threats.
Cybercriminals aren’t looking to play fair against businesses. They don’t care how big or small you are, they don’t care about what services you provide, or what good you offer for the community. You could be a children’s hospital or a single mother selling homemade mittens out of your dining room, you could be a school, an assisted living facility, or a Fortune 500. Either way, your organization is an equally viable target for cybercriminals.
With Cybersecurity Awareness Month just around the corner, now seems to be the appropriate time to consider your own business’ cybersecurity. While there are many, many factors that contribute to how protected your business is against threats, one of the most impactful and insidious is how receptive your employees are (or aren’t) to security-centric behaviors.
Cybersecurity is a complicated beast. Not only do you have to be sure that you’re protected from threats coming from outside your business, there are also a few very real threats that can originate from inside your business, too. Both are critical to prevent, which can be quite effectively accomplished via a zero trust approach to your security.
A VPN—or virtual private network—is something that we recommend any business implementing any form of remote or hybrid work to have in their cybersecurity arsenal. Let’s explore why this is by examining what a VPN does, and what any business should seek out in the one they use.
Is your business prepared to handle the many challenges that come from remote work, chief among them security? If you aren’t, then the transition to remote or hybrid operations is going to be a rough one, to say the least. Let’s discuss how you can implement secure remote or hybrid work policies that are sure to protect your business now and in the future.
Network security is a constant problem for many organizations, and it’s mostly because of the many advanced threats that make their homes on the Internet. Businesses who don’t have dedicated IT resources or security professionals do not know how to handle network security or appropriately protect their assets. Let’s examine some of the more common threats that your business should be prepared to address.
It’s easy to see the headlines and think that a major data breach cannot happen to your business, but this is a dangerous mindset to hold. If you aren’t taking cybersecurity seriously these days, then you’re making a huge mistake. You need to implement security measures now before it’s too late.
- 1
- 2